บทความ
— เรื่องเล่าจากประสบการณ์จริง เกี่ยวกับ Architecture, Engineering และการ Ship Software
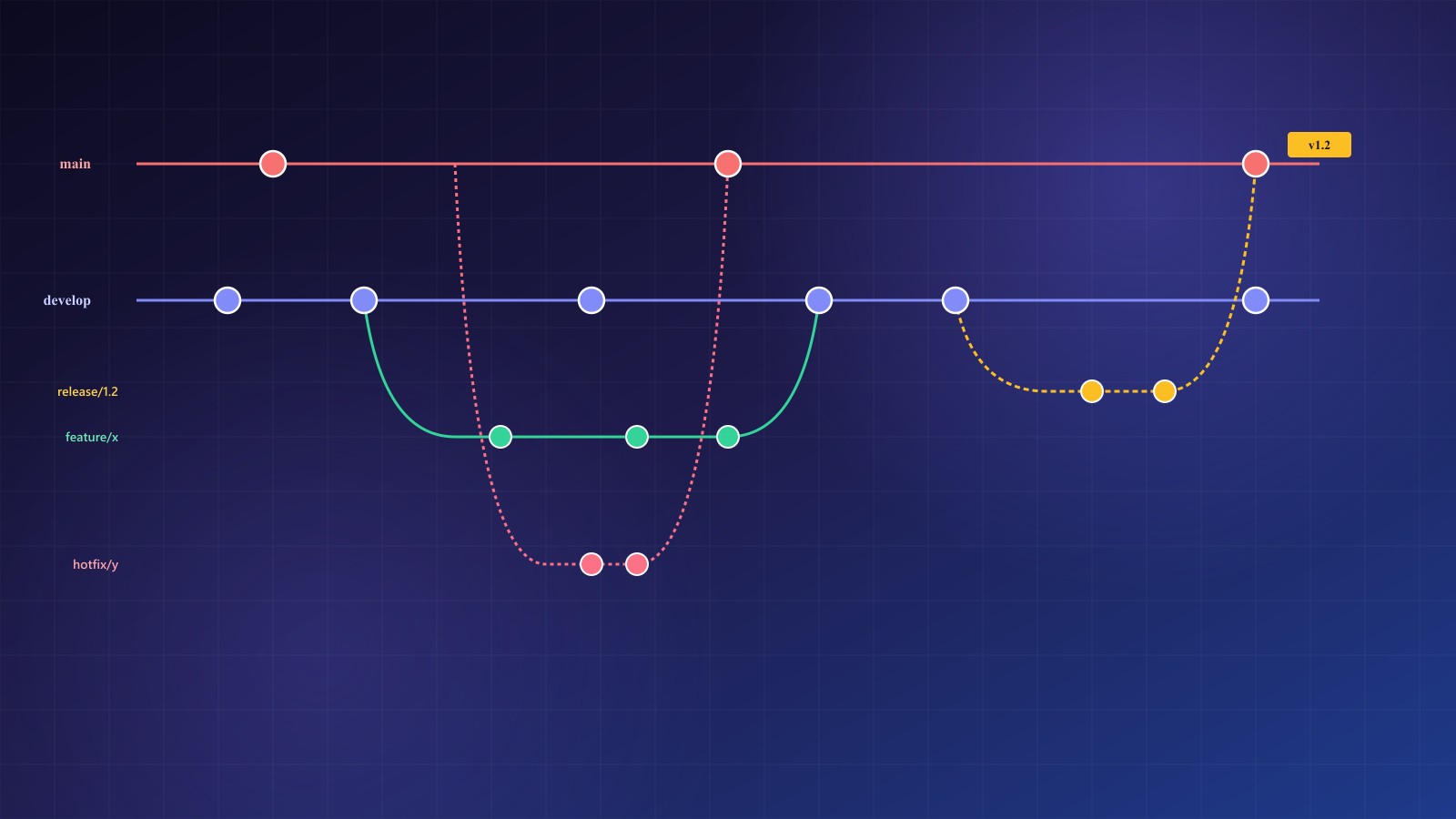
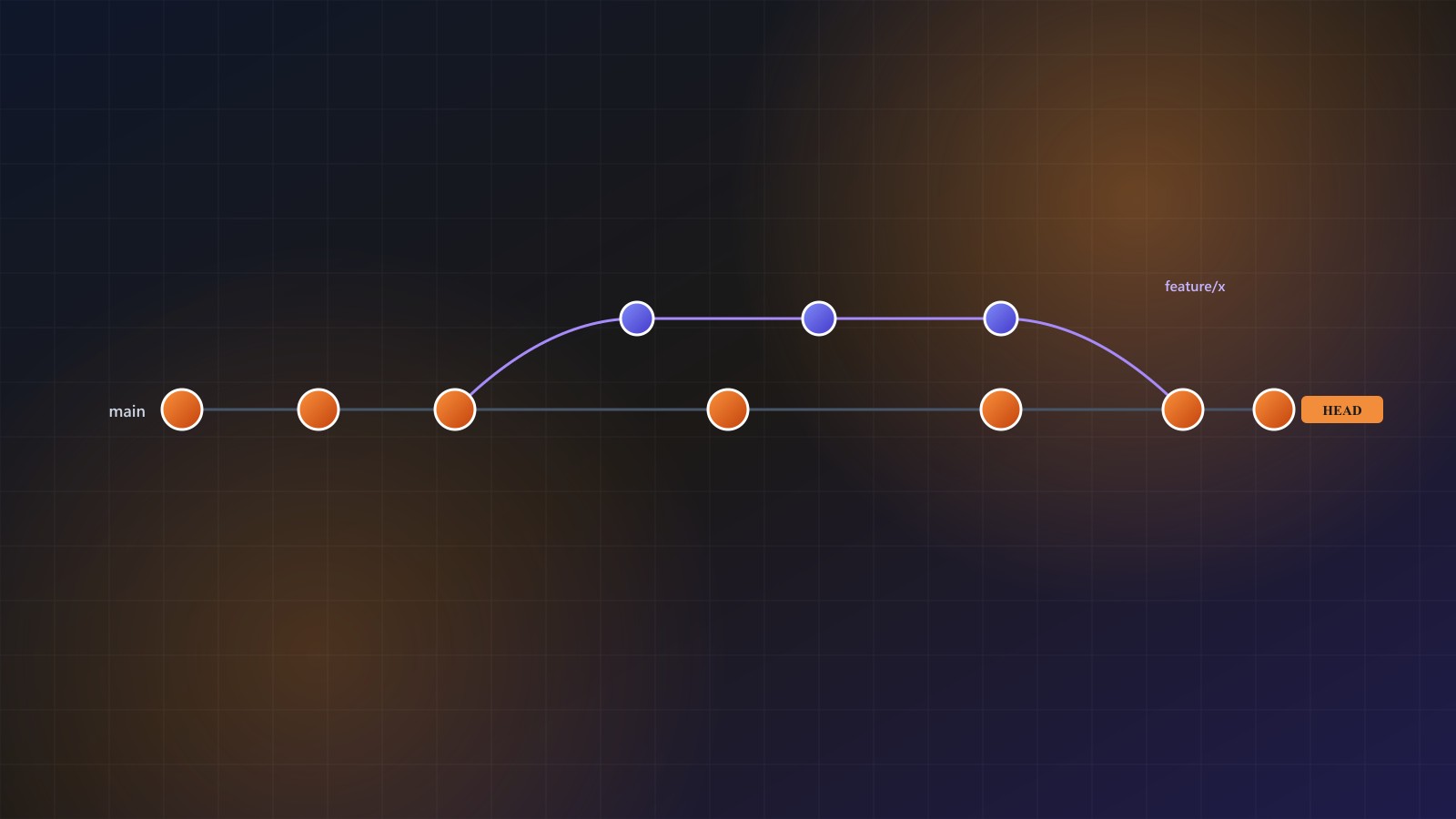
GitFlow and Branching Strategies: Which Workflow Fits Your Team
GitFlow, GitHub Flow, GitLab Flow, and trunk-based development — what each is, when each fits, concrete branch diagrams, the release ceremonies they imply, and how to actually pick one in 2026.
More Articles

GitHub Actions for Automated Deployment: A Practical Guide
How to build deploy workflows that are fast, safe, and survive the 3 a.m. incident — secrets, environments, OIDC, caching, rollback, SSH vs runner-based, and the anti-patterns that catch every team once.
Basic Git Commands Every Software Engineer Should Know
The thirty-something git commands you actually use day-to-day — staging, branching, merging, rebasing, recovering from mistakes, and the small set of aliases worth setting up once.

The PMBOK Situations Playbook: What to Do, What to Change, What to Write Down
Real project-management situations — scope creep, budget cuts, people leaving, vendors failing, deadlines shifting, compliance landing — each with step-by-step moves, the exact documents that must change, and best/worst case outcomes.

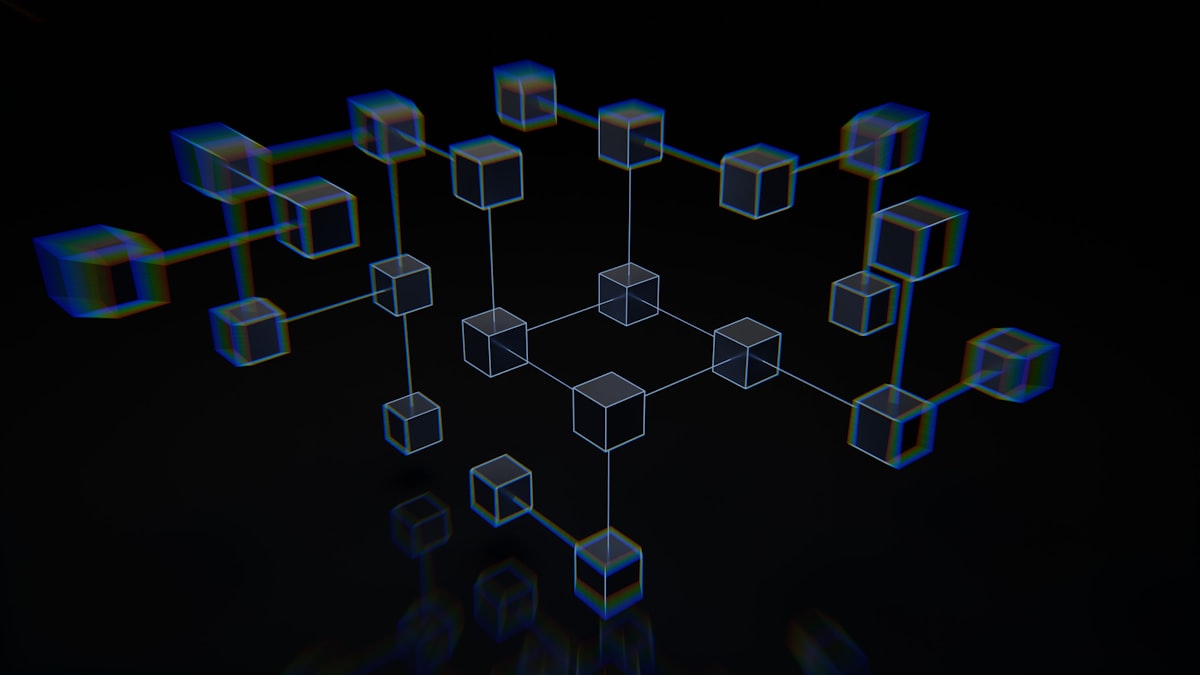
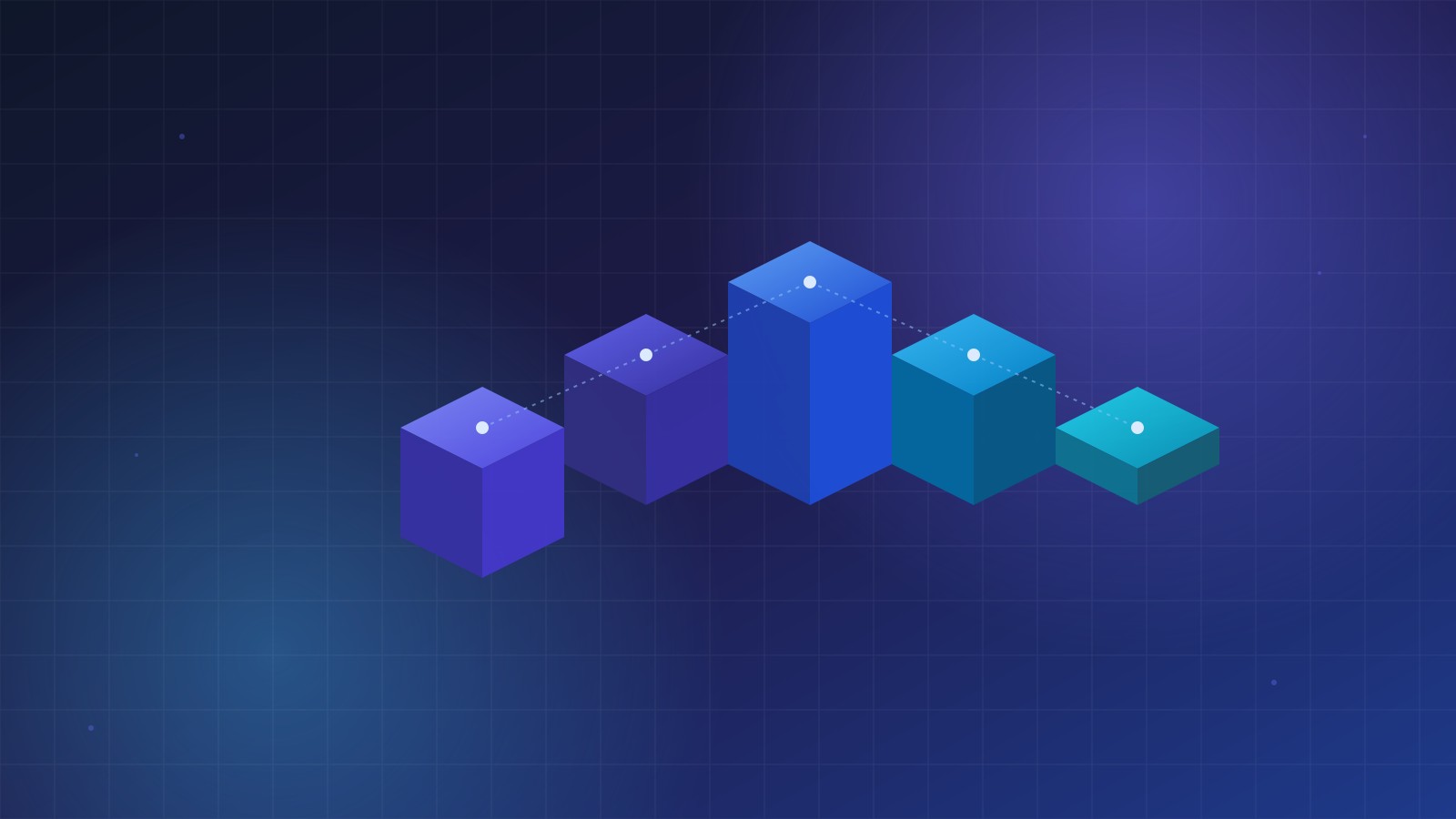
Blockchain from Scratch: A Technical Intro with a Toy App You Can Actually Run
A ground-up, technical introduction to blockchains — hashes, blocks, Merkle trees, proof-of-work, consensus — paired with a ~200-line TypeScript toy chain you can run, fork, and break. The version of the explanation that assumes you're a developer, not an investor.

Flowchart Diagrams: A Practical Guide to Every Symbol and When to Use It
A structural, symbol-by-symbol guide to flowcharts — ANSI/ISO 5807 shapes with real meanings, when each one applies, how to lay out process, swim-lane, and data-flow diagrams, and ready-to-copy Mermaid examples.
Kafka for Beginners: What It Is, When to Use It, and Producer/Consumer Examples in Java, Python, Node.js, and Go
A ground-up introduction to Apache Kafka — what it actually is, the handful of features that matter, the use cases it's genuinely good at, and working producer/consumer snippets in four languages so you can run your first topic in under ten minutes.

PMBOK as a Framework: Inputs and Output Artifacts for Every Part of a Project
A practitioner's walk through PMBOK — the five process groups, the ten knowledge areas, and, for each part, the inputs that feed it and the artifacts that come out. The bits you actually keep on a shelf.

Redis for Beginners: What It Is, When to Use It, and Client Examples in Java, Python, Node.js, and Go
A ground-up introduction to Redis — what it actually is, the handful of data structures that matter, the use cases it's genuinely good at, and working client snippets in four languages so you can run your first cache, queue, and pub/sub in under ten minutes.

Security Attacks Every Engineer Should Know: A Field Guide to the Techniques Attackers Actually Use
A structural, named-technique-by-named-technique walkthrough of the attacks a modern web application has to defend against — injection, authentication flaws, XSS, CSRF, IDOR, SSRF, deserialization, race conditions, supply-chain attacks, and more — with how each works and what to do about it.
SOLID Principles Explained for Working Developers
Five principles that separate code you can still touch in six months from code that becomes a minefield. Each principle explained in plain English with before/after code in TypeScript, Java, Python, and C#.